What Is the L2TP VPN Protocol?
DataProt is supported by its audience. When you buy through links on our site, we may earn a commission. This, however, does not influence the evaluations in our reviews. Learn More.
An unspoken techie rule goes: Out with the old, in with the new. We’re constantly being offered newer and improved software solutions designed to be safer and better suit our needs. However, some pieces of software keep defying the ravages of time, and L2TP is one of them.
L2TP or Layer 2 Tunneling Protocol is a VPN protocol that’s been around since 2000 and is still very much available. Since then, VPN technology has made great strides in providing faster and more secure protocols. However, L2TP still has a couple of aces up its sleeve, which we’ll discuss in this article.
The Short History of the L2TP protocol
L2TP was built upon Microsoft’s Point-to-Point Tunneling Protocol (PTPP), and it’s employed by internet service providers (ISPs) to enable VPN connections.
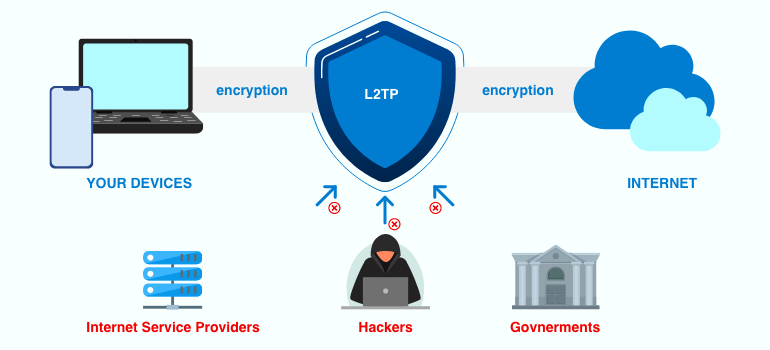
As a series of digital communication procedures, L2TP is only used to offer tunneling capabilities. It gathers user data via private transportation and sends it over public networks. In combination with IPSec, a Layer 3 protection protocol, L2TP provides confidentiality and encryption for VPN functionality.
L2TP was developed by Microsoft and Cisco with the goal to use it as a replacement for the PTPP. It was published in 1999/2000 as the RFC 2661 protocol.
The technology behind this protocol relied on two older tunneling protocols used for establishing a point-to-point connection. The first protocol was Microsoft’s Point-to-Point Tunneling Protocol (PPTP), while the second was Cisco’s Layer 2 Forwarding Protocol (L2F).
In 2005, a new protocol version, L2TPv3, provided enhanced encapsulation, more security options, and carried data links in new ways.

How It Works
L2TP allows for tunneling L2 traffic via an IP network or L3 network. L2 and L3 here refer to the second and third levels in a seven-layer OSI, a telecommunication and computer standardization model. L2 is the Data Link layer, while L3 is the Network Layer. L3 works atop L2, which runs over L1, the Physical Layer.
It all starts when L2TP connection is established between the protocol’s two endpoints – the L2TP Access Concentrator (LAC) and the L2TP Network Server (LNS). Once these two are connected and the L2TP tunnel is created, a PPP link layer is enabled, encapsulated, and sent over the internet.
After this, the PPP connection is established by the end-user with the ISP. When the LAC accepts this connection, the PPP link is up and running. A free slot within the network is assigned, and the request moves on to the LNS.
When this connection is fully authorized and active, a virtual PPP interface appears and the passage of link frames through the tunnel can begin. The LNS accepts the frames, removes their encapsulation, and processes them further as regular frames.
Components of an L2TP Configuration
There are two primary components of L2TP: a tunnel and a session. The tunnel allows secure transport between two L2TP control connection endpoints. Through it, you can only send and receive control packets.
The other significant component – the session – is responsible for carrying user data through the tunnel. One tunnel can contain more than one session. In that case, session identifier numbers keep user data separate.
L2TP/IPSec Combination for Enhanced Security
L2TP by itself uses no encryption or authentication methods despite being an evolutionary step forward from PPTP. L2TP’s primary purpose is to establish a VPN tunnel. For encryption, it has to be bundled with other technologies, such as IPSec.
IPSec is a strong security protocol that employs a robust AES encryption cipher. This protocol also relies on double encapsulation as an additional method of data protection.
As for IPSec’s level of security, the Snowden leaks have revealed that the NSA was trying to crack or weaken this protocol as part of its Bullrun program. While none of these allegations have been proved to be accurate, it is something every VPN user should take into account when thinking about their data security and choosing their VPN protocol.
The L2TP/IPSec VPN connection starts with the IPSec security association (SA) negotiation that usually goes through Internet key exchange (IKE) and UDP port 500. This connection needs a shared password, an X.509 international telecommunication certificate, or a public key.
Afterward, this protocol creates an Encapsulated Security Payload (ESP) that allows devices on both sides to determine where the data comes from. Then L2TP creates a tunnel between the connection endpoints, and data is packed twice: originally by L2TP, then by the IPSec protocol.
To enhance security, most VPNs will offer L2TP bundled with IPSec.
L2TP Passthrough
An L2TP connection needs to go through a router to access the web and transfer its traffic. Passthrough is a router feature you can use to activate or deactivate L2TP traffic on your router.
Another instance where this technology is used is with Network Address Translation (NAT). This feature allows many internet-connected devices attached to a single network to use a single IP address and connection. The issue is that NAT doesn’t work well with L2TP. However, enabling L2TP Passthrough on your router will solve this problem.
Benefits and Drawbacks of L2TP
Before we move on to comparisons of L2TP with other VPN protocols, we’ll sum up some of its main pros and cons.
On the one hand:
- L2TP alone or in combination with IPSec is very easy to set up: If you’re using macOS or Windows operating system, just go to the Network Settings to quickly configure your L2TP connection or an L2TP/IPSec VPN connection.
- L2TP comes preinstalled on Windows and macOS systems: You can set the connection manually or automatically in a few easy steps on these operating systems. It’s also available on other operating systems and devices.
- L2TP combined with IPSec provides a strong level of security: As we’ve mentioned earlier, L2TP on its own doesn’t encrypt and authenticate data. It’s almost always bundled with IPSec, which offers a decent level of security.
On the other hand, however:
- L2TP might be compromised: Although there’s no substantial evidence to support this claim, leaks suggest that the NSA and FBI have weakened or cracked this protocol with backdoors, side-channel keys, or zero-day exploits.
- L2TP on its own is unsafe: This protocol can achieve fast speeds, however, those speeds come at the cost of having no means of encryption or authentication.
- L2TP/IPSec is slower due to the double encapsulation feature: This option encapsulates data twice, which increases its toll on device resources.
- If not set correctly, the NAT firewall can easily block L2TP: You’ll need L2TP Passthrough to avoid NAT firewall stopping L2TP traffic.
Top 3 VPNs Offering the L2TP Protocol
Both Windows and Mac operating systems provide native support for L2TP, making it a widely accessible VPN protocol. And precisely because of this, L2TP is still often offered by various VPN services.
1. ExpressVPN
As one of the best VPN services, ExpressVPN supports L2TP as a legacy protocol for Windows and macOS. L2TP provided us with low ping – which is great for competitive multiplayer games – and up to 65 Mbps, which was enough for quick downloads.
The protection measures ExpressVPN uses include the powerful AES 256-bit and wolfSSL encryption, along with SHA512 hash authentication and 4096-bit DHE-RSA keys.
2. PrivateVPN
PrivateVPN is another VPN that offers L2TP protocol support. It has over 200 available servers, and you can reach decent download speeds with it, with our test machine reaching 60 Mbps, although that speed might vary depending on the location of the server.
PrivateVPN allows for P2P file sharing, with unlimited bandwidth and a no-logs policy that preserves user privacy. This VPN provider recommends using the L2TP protocol as the best way to browse the internet from China without getting blocked by the Great Firewall.
3. PIA
Private Internet Access offers L2TP/IPSec protocol support with UDP and TCP connections. The connection speeds were excellent overall. PIA comes with a daemon that removes all traces of your connection data, latest encryption tools, and blockers for malware, ads, and more.
How Does L2TP Stack Up to Other Protocols?
L2TP on its own is not enough to protect your data. Hence most VPN companies offer it in combination with IPSec. Let’s check how it fares in comparison to other popular protocols.
L2TP vs. PPTP
As its successor, L2TP has better security than PPTP thanks to its IPSec pairing. PPTP uses 128-bit encryption and inferior Microsoft Point-to-Point Encryption (MPPE), while L2TP/IPSec has 256-bit encryption and military-grade AES ciphers.
Additionally, we know that the NSA managed to crack PPTP, while the same can’t be said with certainty about L2TP, although there are some allegations that it happened.
Performance-wise, PPTP is significantly quicker than L2TP. It’s also less stable, since blocking it with firewalls is extremely easy. On the other hand, L2TP uses UDP, and VPN providers can modify the protocol to avoid L2TP being blocked by firewalls.
L2TP vs. IKEv2
IKEv2 is another tunneling protocol based on IPSec, which is why many VPN companies offer it in an IKEv2/IPSec combo. However, IKEv2 is more secure than L2TP/IPSec thanks to several factors.
First of all, IKEv2 hasn’t been – to the best of our knowledge – cracked by the NSA.
Just like L2TP, IKEv2 was created by Microsoft and Cisco. However, there is an open-source version of this tunneling protocol many users consider more trustworthy.
Thanks to the Mobility and Multihoming Protocol (MOBIKE), IKEv2 is more stable and reliable than L2TP. MOBIKE makes this protocol resistant to network changes: You can switch from a Wi-Fi connection to your data plan without losing the VPN connection.
L2TP vs. OpenVPN
OpenVPN takes the lead in this comparison, thanks to the fact it’s open-source, employs SSL 3.0, and you can configure it for more protection. The off-trade is that all this protection makes OpenVPN slower than L2TP.
OpenVPN is more stable than L2TP since it can use any port, including the port for HTTPS traffic, making it very easy to avoid ISP tracking or network admin and ISP firewalls.
L2TP does come out victorious as a more accessible type of connection since it comes integrated into many operating systems. Setting up OpenVPN, on the other hand, can be a complex task unless VPN software handles it for you.
L2TP vs. SSTP
Secure Socket Tunneling Protocol (SSTP) uses SSL 3.0 and the port for HTTPS traffic, making it a superior solution in terms of stability compared to L2TP. It’s also more resistant to firewall blocking and faster because it doesn’t use double encapsulation.
On the flip side, L2TP is more accessible since SSTP is only natively available on Windows.
L2TP vs. WireGuard
From the get-go, WireGuard beats L2TP with improved security measures such as a new algorithm that users can’t modify to inadvertently endanger their data and its open-source nature.
WireGuard is also much more resistant to firewall blocking since it uses numerous UDP ports, while L2TP, when paired with IPSec, uses only three. It’s faster than L2TP, too, as it doesn’t use double encapsulation.
Both VPN tunneling protocols are very accessible and easy to use on multiple platforms, so no big differences in that department.
L2TP vs. SoftEther
SoftEther is the winner in all categories but one. It employs 256-bit AES encryption, SSL 3.0, and it’s open-source and very stable.
SoftEther acts as both a VPN server and a protocol. As a VPN server, it supports L2TP/IPSec protocol, along with a number of other protocols. Even though it’s packed with security measures, SoftEther is also faster than L2TP since it was explicitly coded with high-speed throughput in mind.
L2TP is easier to use and more accessible. SoftEther is compatible with most operating systems, but setting it up can take some time. For example, your VPN app might support SoftEther, but you’d still have to download and install SoftEther software.
Out With the Old?
The main reason L2TP/IPSec is still widely supported is that it’s readily available. It offers decent protection when used with IPSec, albeit at the expense of diminished connection speed.
However, VPN technology has come a long way since the 2000s, when L2TP first appeared. WireGuard and SoftEther, for example, are newer protocols that’ll give you more if you’re willing to invest some time and effort into setting them up.


