How to Stop a WebRTC Leak on Your Favorite Browser
DataProt is supported by its audience. When you buy through links on our site, we may earn a commission. This, however, does not influence the evaluations in our reviews. Learn More.
As we have moved so much of our lives online, privacy has become a priority. For that particular reason, we at DataProt advise using one of the recommended VPN services to protect your information and privacy. However, not everything can be solved with a gadget-like extension or app. It’s important to familiarize yourself with potential breaches and vulnerabilities some VPNs have; a WebRTC leak is one of the most common ones.
WebRTC: What Is It and Why It’s Useful
WebRTC (Web Real-Time Communication) is open-source software that’s free to use and add through JavaScript APIs (Application Programming Interface) to allow for video and audio communication through P2P (peer-to-peer) protocols.
The technology reduces video and audio lagging, even for large files. WebRTC is an excellent choice for software enabling group calls and webinars with improved sound quality. Now that we have answered: “What is WebRTC?” we’ll move on to analyzing why it represents a potential privacy issue.
WebRTC and IP Address Leaks
WebRTC is supported by modern browsers like Chrome, Firefox, Safari, Opera, Brave, Edge, etc. Because of browser vulnerabilities, leaving your public IP address unprotected may cost you your anonymity through a WebRTC STUN (Session Traversal Utilities for NAT) server request, even though your VPN is properly functioning.
Windows makes it possible to send data over routes that weren’t set up as the default ones, and a STUN server sends requests to any interface it can reach from the user’s side. A UDP packet can sometimes include your actual IP address, and a WebRTC IP leak is the result of that.
Testing for Leaks
Thankfully, plenty of services online test for potential leaks so you can diagnose your VPN. According to our tests, ExpressVPN prevents IP leaks and has an online service for checking if WebRTC is enabled and if the IP address is encrypted and tunneled through VPN. Websites like BrowserLeaks test WebRTC as well, and you can get an in-depth report.
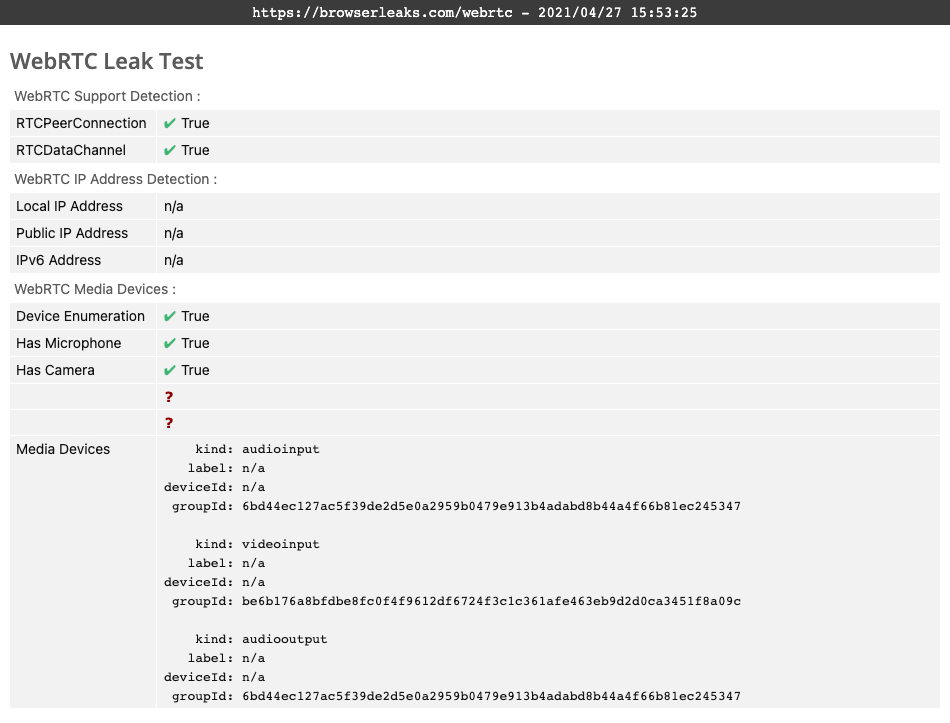
If your VPN service is working correctly, your report should show something similar to the one displayed here.
How to Prevent a WebRTC Leak in Chrome
The most straightforward way of preventing WebRTC from leaking your IP address is to use a VPN with a Chrome extension. However, if you are not looking to solve the leak issue with a VPN service, you need to know that you can’t disable it manually. Instead, you will have to use an external solution. While VPN extensions are more reliable, there are few free non-VPN options available. Also, keep in mind that, besides dealing with WebRTC, these extensions don’t protect your privacy further.
WebRTC Leak Shield
This is a Chrome browser extension with a simple interface, as you can see from the screenshot.
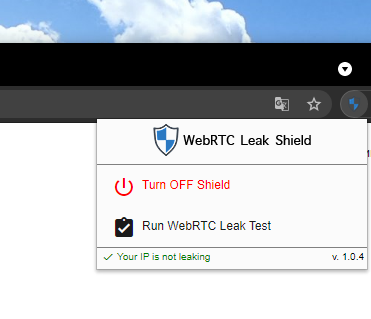
The only options available are to turn the shield on or off and run the extension’s leak test. After conducting a few tests of our own, we found that the extension reliably shielded us from public IP address leaks through WebRTC services. However, unlike a VPN, the extension doesn’t encrypt your connection, nor does it hide your IP address during your online browsing experience. This is something you need a virtual private network for.
The extension is also available for Microsoft Edge users and can be found on the Microsoft Edge Add-ons page.
WebRTC Leak Prevent
This is another go-to solution a large number of Chrome users prefer. When you add the extension to Chrome, it will present you with a few options.
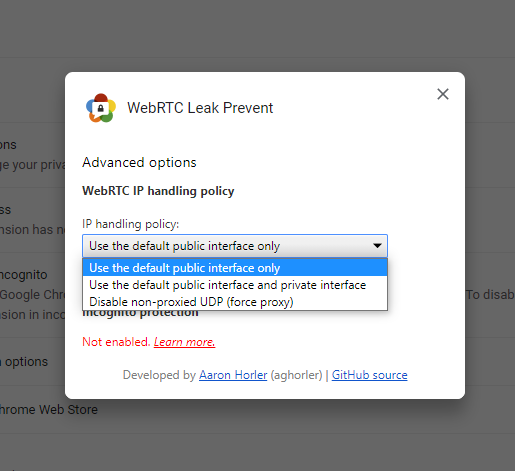
The first option that uses the default public interface will route WebRTC traffic directly through the VPN adapter. The second option will also use the default network adapter for your local network. The third option forces the use of a proxy and only allows for WebRTC traffic over UDP proxies. It can also affect your WebRTC communication and can end up disabling it altogether for some users.
Stopping a WebRTC Leak in Firefox
Unlike Chrome, Firefox does allow for these WebRTC related settings to be changed within the browser. It just takes three simple steps:
- After opening Firefox, enter “about:config” in the URL bar.
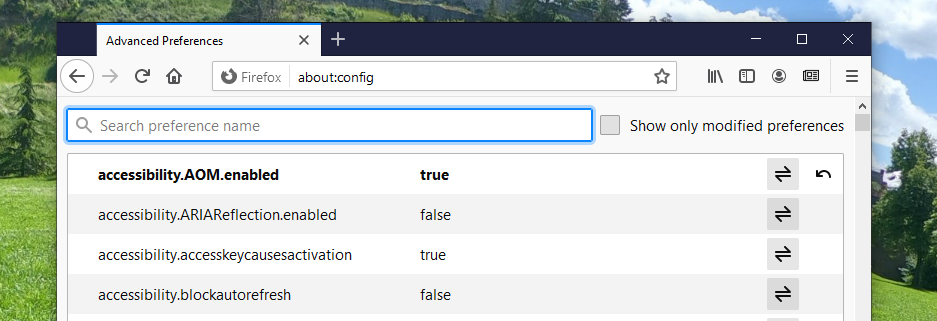
- The setting you need to search for is “media.peerconnection.enabled”.

- Now double-click the entry, or single-click the arrows on its right to change the setting to false.

Remember to check these settings regularly after updating Firefox, since updates can sometimes revert it to default, i.e., turn it back on.
How to Disable WebRTC in Safari
Safari takes a more cautious approach than Chrome and Firefox by blocking camera and microphone access by default. Therefore, the only potential leak you need to worry about with this Apple product is not that severe. To turn off WebRTC, you will need to do the following:
- Open Safari;
- Open Preferences and find the Advanced tab;
- Check the option that says “Show Develop menu in menu bar.”
- From the Develop drop-down menu, go to WebRTC;
- Mark the option called “Disable Legacy WebRTC API.”
How to Disable WebRTC on Android and iOS
Android
The option for disabling WebRTC directly through the Android version of Chrome isn’t currently available. We have tested solutions that have worked for previous versions of the browser, but with our test phone running on Android 11 and Chrome version 90.00.4430.82, it wasn’t possible.
At DataProt, for that particular reason, we recommend using a dedicated Android VPN. Users with a tendency of connecting to public Wi-Fi need to think about their security and privacy even more.
iOS
Unfortunately, the situation with iOS is similar to Android. To prevent a WebRTC Leak, you will have to see what VPN for iOS is the best fit for your needs.


