What Are Obfuscated Servers, and Why Do You Need Them?
DataProt is supported by its audience. When you buy through links on our site, we may earn a commission. This, however, does not influence the evaluations in our reviews. Learn More.
If you are reading these lines, you likely have a general sense of what a VPN is but may not know the specifics. You probably already know that a VPN server can hide your identity and give you access to usually blocked content.
All that is possible thanks to the VPN servers, but what are obfuscated servers? Essentially, obfuscated servers are designed to conceal your use of a VPN service. While this may seem minor, it’s an essential feature for users who need to obscure their online activity for privacy reasons.
In this article, we’ll explain what obfuscated servers are and how they can help you protect your privacy online.
What Are VPN Obfuscated Servers?
Before we start explaining, you should know that an obfuscated server isn’t a server per se. It’s a protocol designed to conceal the fact that you are using a VPN in the first place.
It won’t make much sense if you have to connect to the server before your traffic gets encrypted. Your internet service provider (ISP) could easily keep track of you and stop you from connecting to the server in the first place. This would make VPN obfuscation useless.
The whole confusion about the server is related to how each VPN provider calls this feature. For example, NordVPN refers to it as the obfuscated server, while Surfshark calls it NoBorders. It’s also known as cloaking, obfuscation, scrambling, and stealth technology.
We’ll still refer to them as obfuscated servers throughout the article, but keep in mind this is a protocol. Read on to learn how it all works.
What Is an Obfuscated VPN Server?
To understand obfuscation, you must know how a Virtual Private Network works. When you connect to a VPN server, your traffic goes through an encrypted tunnel. ISPs and governments use Deep Packet Inspection to examine your internet traffic data and monitor what you can access. With DPI’s help, your ISP can’t track or monitor your online activities, but they know you are using a VPN.
Now, if you live in one of the heavily censored nations, the government can automatically block VPN traffic, and you can get arrested for using a VPN in the first place. To get around this, some VPN providers offer obfuscated servers.
Your VPN’s obfuscated servers make it look like your encrypted data packets are just regular traffic. Your traffic is still encrypted, but VPN protocols disguise it to fool DPI. It’s important to remember that if a human being looks closely at your data packets, they should be able to see through VPN obfuscation.
How Does VPN Obfuscation Work?
Now that you know what an obfuscated server is, let’s take a closer look at how it works.
As we mentioned, when you connect to a VPN server, your traffic goes through an encrypted tunnel. The problem is that some governments can still detect and block VPN traffic. VPN obfuscation is a protocol that uses different methods to make your encrypted traffic look like regular internet traffic or make it unrecognizable as a VPN or anything else.
Most providers also offer features like DNS leak protection and a kill switch to improve privacy and security further. By sending all DNS requests through the VPN server, DNS leak protection stops your ISP from keeping track of what you do online. On the other hand, a kill switch ensures that your traffic is always protected by the VPN, even if the connection drops.
Some of the most common methods employed by providers of the best VPNs with obfuscated servers are:
- OpenVPN Over SSL/SSH
- OpenVPN Scramble or XOR Obfuscation
- SOCKS5 Proxy or ShadowSocks
- Obfsproxy
OpenVPN Over SSL/SSH
OpenVPN is the most common protocol used by VPN providers for regular encrypted packet transfer. The issue is that DPI can easily detect and stop such traffic.
With some help from the open-source software stunnel, a VPN adds a Secure Sockets Layer (SSL) or Transport Layer Security (TLS) encryption layer and disguises your traffic to look like regular HTTPS traffic. It also helps since HTTPS traffic already flows on both layers, removing further suspicion.
You should know that setting up stunnel isn’t simple and must be done on your and the server’s end. For that reason, most VPN companies don’t offer it by default.
OpenVPN Scramble or XOR Obfuscation
An OpenVPN scramble is another way of using already established infrastructure to turn a regular VPN protocol into an obfuscated VPN server protocol. It uses an XOR chipper to turn your data packets into a bunch of nonsense that is impossible to read without a decrypting key.
An XOR chipper on its own isn’t impossible to intercept and break. It uses a weak encryption key, which can be easily broken with the help of frequency analysis. So alone, it doesn’t provide good enough protection, but in combination with OpenVPN, you get decent encryption. OpenVPN encrypts your data, and XOR encrypts everything to prevent DPI from recognizing data packages as VPN traffic.
SOCKS5 Proxy or ShadowSocks
SOCKS5 and ShadowSocks are tools used in tandem to provide VPNs with obfuscated server capabilities. SOCKS5 is an internet protocol that routes communication between a client and a server through a proxy, while ShadowSocks is an open-source encryption protocol.
You can immediately spot the problem: None of them can work independently. SOCKS5 doesn’t encrypt your traffic, so it can still be detected by DPI. To remedy this, VPN providers combine it with ShadowsSocks encryption to provide the much-needed obfuscation part.
There is just one downside. Just like OpenVPN over SSL/SSH, it requires additional setup, which regular users can’t do.
Smartproxy – Visit Website
Smartproxy is an award-winning obfuscated proxy provider with global IP coverage with more than 50 million rotating residential IPs in 195 worldwide regions worldwide. The service offers four main proxies: residential, data center, shared, and search engine–– several setups for every user’s unique need. It also features proxies for major cities and states and other valuable applications and extensions for multi-level businesses.
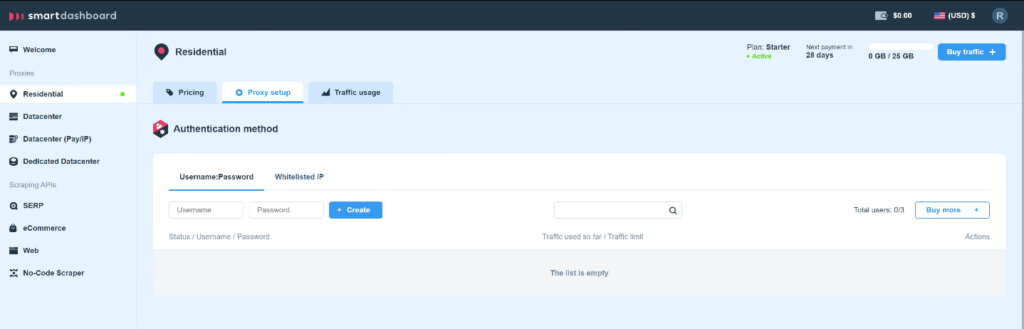
Most users prefer a residential proxy for personal use. To set it up, go to the Proxy Setup section. Authenticate your residential IPs by creating a username and a password or by whitelisting an existing IP.
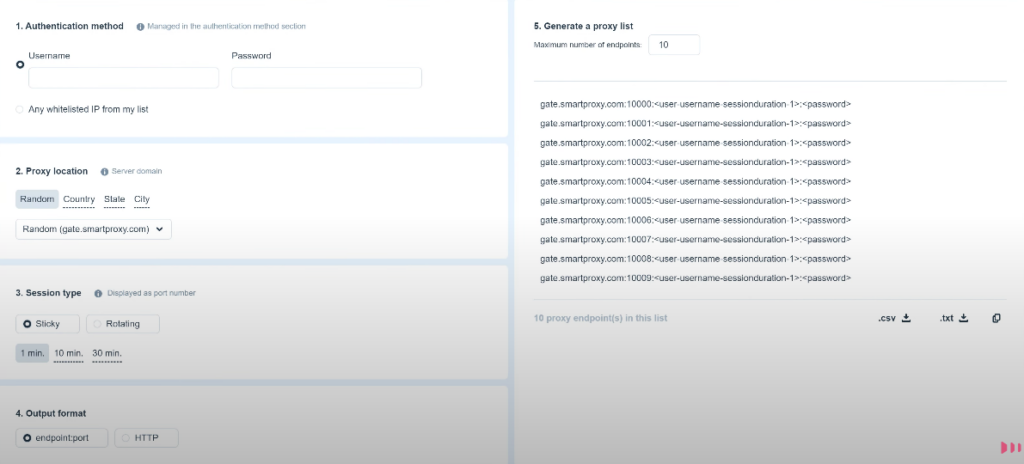
Enter the same credentials that you recently created in the Endpoint Generator block. Select the proxy location of your liking. Then choose a session type that includes the duration of the proxy usage. Set a Preferred Output Format, and download the generated proxy list. Lastly, apply the port and endpoints in the list to any application to instantly use the proxies.
Obfsproxy
Obfsproxy, also known as obfuscation proxy, is an open-source tool developed as a subproject of the now famous The Onion Router (Tor) Project. Just like the rest of the obfuscation VPN methods, it adds another layer which tries to mask your VPN encryption as something that is not, in our case, HTTP traffic.
Besides VPN obfuscation, it also uses a randomized byte pattern handshake, which adds a layer of security, but DPI with an entropy test can sometimes spot them, and on top of that, they aren’t easy to set up.
Why Do You Need VPN Obfuscation?
Setting up obfuscated servers isn’t easy, so why would you want one? The reason is that many countries are now cracking down on VPN usage. They throttle or block IP addresses known to belong to VPN providers. If that isn’t enough, here are a few more reasons you should acquire an obfuscation-capable VPN.
- To Bypass VPN Blocks
The most common reason is to bypass VPN blocks. If you live in or travel to a country with internet censorship, like China, Iran, Russia, or Turkey, you know that using a VPN isn’t always easy. That’s where VPN obfuscation comes in handy since it can bypass most of the DPI that is looking for and blocking VPN traffic.
- To Get Around Geo-Blocks
Another common reason is to get around geo-blocks. Just like some countries block VPNs, many streaming services, like Netflix and Hulu, also block VPN traffic. I doubt it will surprise you to learn that more than half of VPN users use a VPN to access Netflix.
The most common way they do it is by detecting and blocking IP addresses known to belong to VPN providers, which Hulu is notoriously known for. Lucky for you, many VPN services, like NordVPN, can help you access Hulu content blocked in your country or region.
That is why having a VPN obfuscated server can be useful, as it can make it appear as if your traffic is coming from a regular website rather than a VPN. This makes it much harder for streaming services to block your traffic.
- To Avoid ISP Throttling
ISP throttling is when your ISP slows down your internet connection because they don’t like what you’re doing online. This is usually done to stop people from using VPNs or torrenting files.
So, if you use a VPN with an obfuscated server, your ISP won’t be able to throttle your traffic since it won’t be able to recognize it properly. With the right VPN, you can even torrent without your ISP knowing.
- To Protect Your Privacy
Another common reason people use VPNs with obfuscated servers is to protect their privacy. While regular VPNs are good at hiding your identity and location, they aren’t perfect, and with enough time and effort, someone could still figure out who you are and where you’re located.
That’s why using obfuscated VPN servers is a good way to protect your privacy since it makes it much harder for someone to figure out who you are and what you’re doing online.
- To Improve Your Security
Finally, another reason to use obfuscated servers is to improve your security. While regular VPNs are good at encrypting your traffic and keeping your data safe, they can still be intercepted and decrypted by someone with enough time and resources.
However, if you use an obfuscated capable VPN, it will be much harder for someone to intercept and decrypt your traffic since they won’t be able to tell that it’s VPN traffic in the first place.
Best VPNs With Obfuscated Servers
Now that we’ve covered VPN obfuscation and why you may need it, let’s look at some of the top VPN providers and see whether they have obfuscated servers.
NordVPN
You’ve undoubtedly heard of NordVPN if you’ve ever searched for a VPN on Google. NordVPN is one of the most popular VPN companies for a reason. It’s fast, secure, and easy to use, and they’ve invested heavily in marketing. NordVPN also has an extensive network of over 5,600 servers in 60 countries, including obfuscated servers.

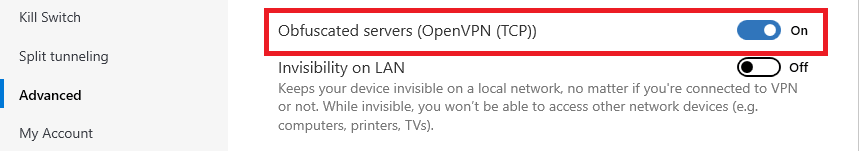
To access NordVPN’s obfuscated servers list, you’ll first have to set the OpenVPN(TCP) or (UDP) protocol. With IKEv2 or NordLynx protocols, the obfuscated servers will be grayed out. Enabling access to NordVPN obfuscated servers is a simple matter. You just need to go to Settings, locate Advanced settings, and turn Obfuscated servers (OpenVPN) on.
ExpressVPN
ExpressVPN is another great VPN provider with obfuscated servers. It offers over 3,000 servers located in 94 countries. We already had a chance to do a full ExpressVPN review and found it was fast, secure, and easy to use.
What’s interesting about ExpressVPN is that there’s no option to choose particular obfuscated servers or even toggle the capabilities on or off. Instead, it automatically activates when it detects a DPI.
Since our government doesn’t monitor internet traffic, we couldn’t check it with Wireshark. Instead, we contacted customer service, who told us their servers and our connection were safe.

ExpressVPN is more than capable of going head to head with Hulu geo-blocking, but we still believe you should have a way of knowing if obfuscation is turned on or not and not find out by bumping against the Great Firewall of China. It would even provide the users themselves with peace of mind, knowing that everything is working as it should.
SurfShark
SurfShark is among the youngest VPN providers, and it quickly rose to the top thanks to its quality, security, and speed. So naturally, you can access obfuscated servers with SurfShark, and unlike with Express VPN, the feature can be found in the program settings. Searching for it in the settings, however, can be a little confusing because the provider doesn’t call it obfuscated technology or servers.
 To enable obfuscated servers on SurfShark, go to Settings > VPN settings and scroll all the way to the bottom, where you’ll find the NoBorders option and turn it on. You don’t need to connect to any specific servers, as with NordVPN; the feature will work on any of SurfShark’s 3,200-plus servers spread across 65 countries.
To enable obfuscated servers on SurfShark, go to Settings > VPN settings and scroll all the way to the bottom, where you’ll find the NoBorders option and turn it on. You don’t need to connect to any specific servers, as with NordVPN; the feature will work on any of SurfShark’s 3,200-plus servers spread across 65 countries.
Conclusion
VPN obfuscation is a great way to get around government censorship and protect your privacy. It’s also a great way to improve your security since it makes it much harder for someone to intercept and decrypt your traffic. If you value your privacy and security, you shouldn’t think twice about getting a VPN with obfuscated servers.


